Audit Your Infrastructure – Install Rudder Server on CentOS 7 / Ubuntu 16.04 / Debian
When the organization grows with a lot of IT devices, it is very challenging to keep them compliance with security standards and to monitor them for noncompliance is a humongous task. With Rudder, it can now be done easily.
Rudder is an open source software solution for IT infrastructure Automation & Compliance. It is straightforward web-based audit and configuration management tool that helps you keep an eye on Infrastructure compliance and achieve 100% compliance with the help of built-in automated rules.
Article Series
1. Audit Your Infrastructure – Install Rudder Server on CentOS 7 / Ubuntu 16.04 / Debian
2. Audit Your Infrastructure – Install Rudder Agent on CentOS / Ubuntu / Debian
3. Audit Your Infrastructure – Perform Security audit using Rudder
Advantage of Rudder
Rudder has built-in rules to perform low-level configuration patterns like ensure file content, ensure package installed, ensure line in a file, etc.
Rudder has two types mode on policy level,
Checked – Just reports the noncompliance.
Enforced – Reports noncompliance and performs the remediation action.
Ruder works on almost every device including physical servers, virtual servers, cloud instances, and embedded IoT devices.
The rudder has the built-in workflow to validate/deploy configuration changes via Change request.
Rudder works as a client-server model. Rudder Agents (CFEngine) send audit data to Rudder server, and it needs to be installed on all hosts to audit. The agent is very small, light-weighted, and auto-updatable.
Features
- Automatic Host inventory
- Full featured Web interface
- Custom Policy editor
- Standardized, reusable policies
- Dynamic generation of per-host policies
- Centralized reporting and historic information for policy applied to hosts
- Grouping based on search queries run against inventory
- Automatic updating of such groups (dynamic groups)
- Change Request / Validation
- REST API
- Git backend
Requirements
Rudder Server
OS
- Debian 7 & 8
- RedHat Enterprise Linux (RHEL) / CentOS 6 and 7
- SuSE Linux Enterprise Server 11 SP1 and SP3, 12 SP1
- Ubuntu 14.04 LTS (Trusty) & 16.04 LTS (Xenial)
Hardware
- A server with at least 2 GB of RAM
- /var file system with at least 50GB of disk space
Ports
- Port 5309, 443 TCP and 514 TCP/UDP from nodes to Rudder Server for agent communication.
- Port 443 from your desktop to rudder Server for accessing the Rudder web interface.
DNS
If you want to trigger agent runs from Rudder Server (apart from regular interval), you will need DNS server to resolve the hostname of your nodes.
READ: How to setup DNS server on CentOS 7 / RHEL 7
Software
Rudder requires Java RE version 8 or later. It will be installed automatically during the installation of Rudder server.
If you want to go for Oracle Java, then follow the below articles.
READ: How to install Oracle Java 8 on CentOS 7 / RHEL 7
READ: How to install Oracle Java 8 on Ubuntu 16.04
READ: How to install Oracle Java 8 on Debian 9
Permission
Switch to the root user.
su -
OR
sudo su -
Here, we will cover the installation of Rudder Server.
Install Rudder Server
Add Rudder Repository
Add the Rudder project package repository for the installation of Rudder server.
### CentOS 7 / RHEL 7 ### # rpm --import https://www.rudder-project.org/rpm-repos/rudder_rpm_key.pub # echo '[Rudder_4.1] name=Rudder 4.1 EL repository baseurl=https://www.rudder-project.org/rpm-4.1/RHEL_$releasever/ gpgcheck=1 gpgkey=https://www.rudder-project.org/rpm-4.1/RHEL_$releasever/repodata/repomd.xml.key' > /etc/yum.repos.d/rudder.repo ### Debian / Ubuntu ### # wget --quiet -O- "https://www.rudder-project.org/apt-repos/rudder_apt_key.pub" | sudo apt-key add - # echo "deb https://www.rudder-project.org/apt-4.1/ $(lsb_release -cs) main" > /etc/apt/sources.list.d/rudder.list # apt-get update
Install Rudder Server
You can use yum in CentOS/RHEL and apt-get in Ubuntu/Debian for installing Rudder Server.
### CentOS 7 / RHEL 7 ### yum install -y rudder-server-root ### Debian / Ubuntu ### apt-get install -y rudder-server-root
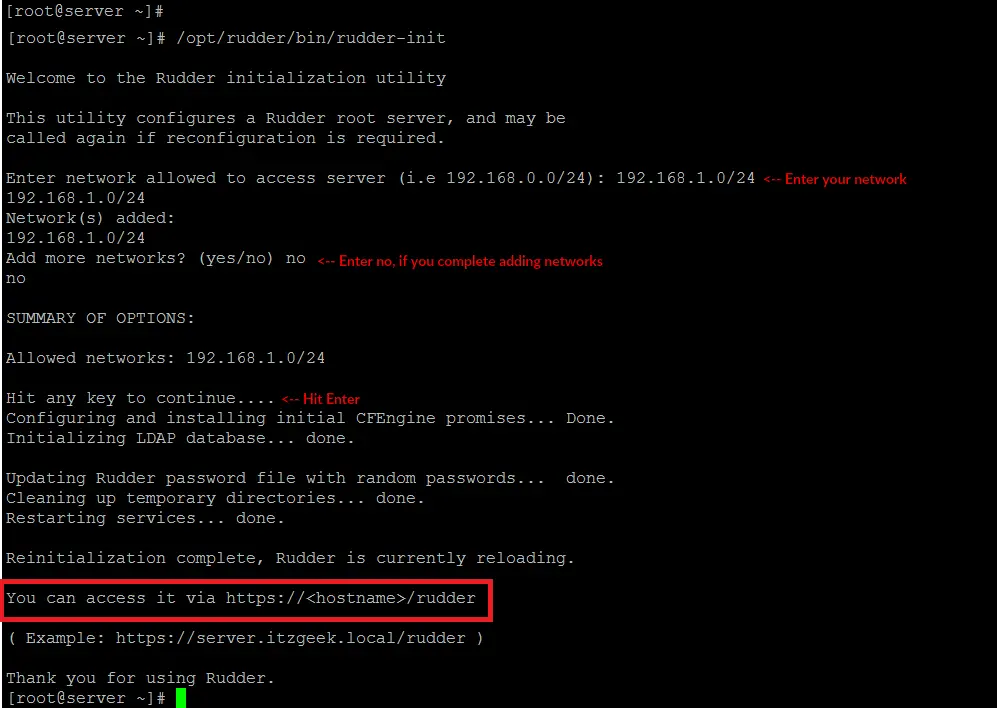
Once the Rudder server installation is complete, you have to run the following command to configure some system elements.
/opt/rudder/bin/rudder-init
Output:
Welcome to the Rudder initialization utility This utility configures a Rudder root server, and may be called again if reconfiguration is required. Enter network allowed to access server (i.e 192.168.0.0/24): 192.168.1.0/24 <-- Enter your network 192.168.1.0/24 Network(s) added: 192.168.1.0/24 Add more networks? (yes/no) no <-- Enter no, if you complete adding networks no SUMMARY OF OPTIONS: Allowed networks: 192.168.1.0/24 Hit any key to continue.... <-- Hit Enter Configuring and installing initial CFEngine promises... Done. Initializing LDAP database... done. Updating Rudder password file with random passwords... done. Cleaning up temporary directories... done. Restarting services... done. Reinitialization complete, Rudder is currently reloading. You can access it via https://<hostname>/rudder ( Example: https://server.itzgeek.local/rudder ) Thank you for using Rudder.
Firewall
Update firewall rules for Rudder.
FirewallD:
firewall-cmd --permanent --zone=public --add-port=5309/tcp firewall-cmd --permanent --zone=public --add-port=5310/tcp firewall-cmd --permanent --zone=public --add-port=443/tcp firewall-cmd --permanent --zone=public --add-port=514/tcp firewall-cmd --permanent --zone=public --add-port=514/udp firewall-cmd --reload
UFW:
ufw allow 5309/tcp ufw allow 5310/tcp ufw allow 443/tcp ufw allow 514/tcp ufw allow 514/udp ufw reload
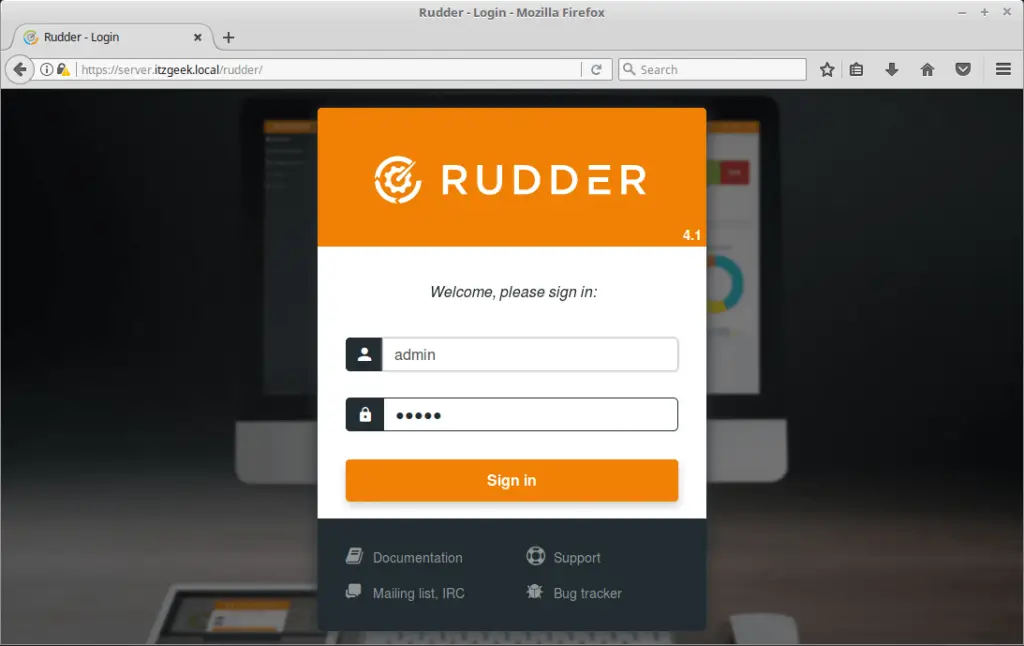
Access Rudder Web Interface
Now, you will be able to access the Rudder web interface by going to below URL.
OR
On Rudder login screen, enter the username and password to access the Rudder dashboard.
The default login is “admin” with password “admin”.
Dashboard may look like this,
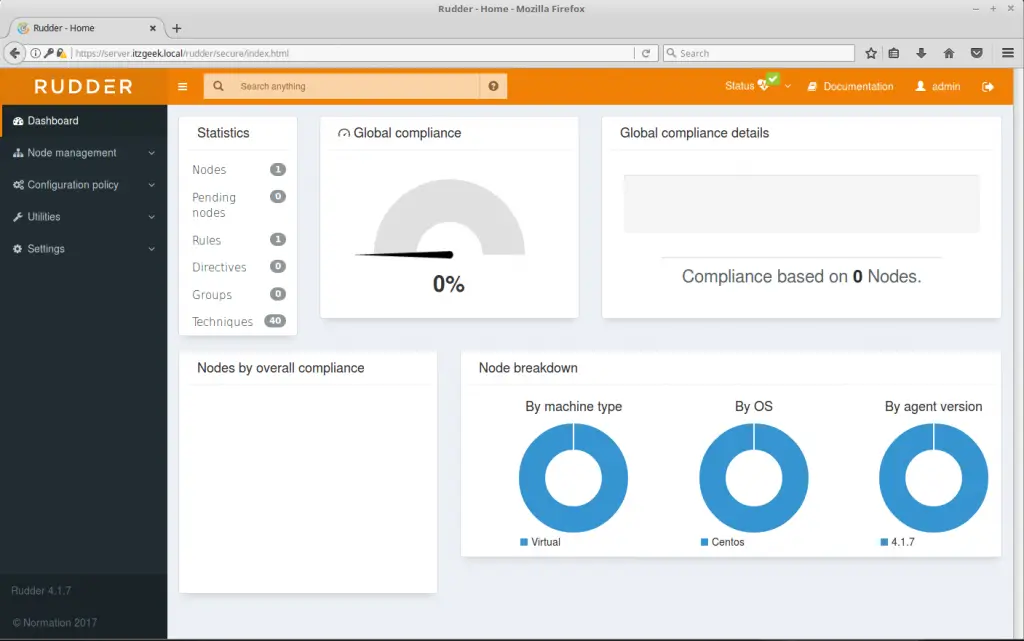
That’s All. In the next article, we will cover the installation of Rudder agent on nodes to collect the compliance data.
