How To Setup Let’s Encrypt SSL Certificate with Nginx on Debian 10 / Debian 9
Let’s Encrypt is a certificate authority that provides free SSL certificates for TLS encryption, launched in April 2016.
Let’s Encrypt is not only provides SSL certificates; it also automates certificate creation, validation, signing, implementation, and renewal of certificates for secure websites.
Currently, Let’s Encrypt supports auto installation of certificates on Apache, Nginx, Plex, and Haproxy.
Prerequisites
I recommend you to set up LEMP stack on your system before you proceed further.
READ: How to Install LEMP Stack on Debian 10
READ: How to Install LEMP Stack on Debian 9
Setup Let’s Encrypt SSL Certificate with Nginx
Install Certbot
To generate a certificate for your domain, you should have terminal access and Certbot ACME client. Certbot client handles certificate issuance and installation with no downtime.
Certbot is available on Debian base repository. So, you can use below commands to install it.
sudo apt update sudo apt install -y certbot python-certbot-nginx
Create Virtualhost
We will now create a virtual host for the domain www.itzgeek.net.
sudo nano /etc/nginx/conf.d/www.itzgeek.net.conf
Use the below information.
server {
server_name www.itzgeek.net;
root /opt/nginx/www.itzgeek.net;
location / {
index index.html index.htm index.php;
}
access_log /var/log/nginx/www.itzgeek.net.access.log;
error_log /var/log/nginx/www.itzgeek.net.error.log;
location ~ \.php$ {
include /etc/nginx/fastcgi_params;
fastcgi_pass 127.0.0.1:9000;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME /opt/nginx/www.itzgeek.net$fastcgi_script_name;
}
}
Create a document root to hold HTML files.
sudo mkdir -p /opt/nginx/www.itzgeek.net
Change the permission of the directory.
sudo chown -R nginx:nginx /opt/nginx/www.itzgeek.net
Place the sample HTML file in the document root of your domain.
echo "This is a test site @ www.itzgeek.net" | sudo tee /opt/nginx/www.itzgeek.net/index.html
Restart the Nginx service.
sudo systemctl restart nginx
Create / Update DNS Record
Access your DNS management tool or Domain registrar and create an A/CNAME record for the domain. Ex: www.itzgeek.net.
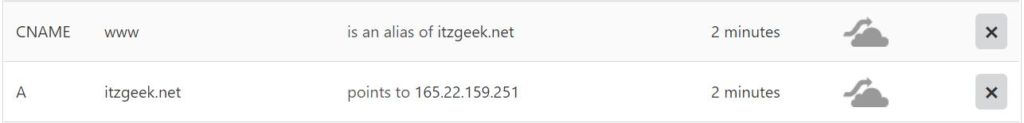
Wait for some time to let the record propagate.
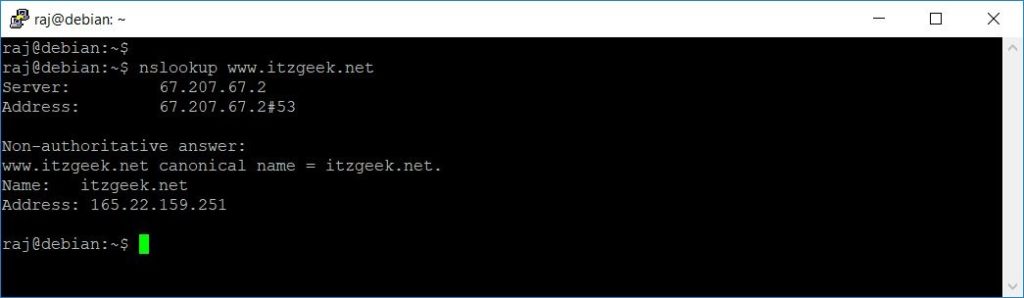
Check the DNS propagation with Nslookup sudo apt install -y dnsutils utility.
Install Let’s Encrypt Certificate
Use the certbot command to create a Let’s Encrypt certificate and configure Nginx to use the certificate.
sudo certbot --nginx
Follow the interactive prompt and install the certificate.
Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator nginx, Installer nginx Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): [email protected] << Enter Email ID - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must agree in order to register with the ACME server at https://acme-v02.api.letsencrypt.org/directory - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (A)gree/(C)ancel: A << Agree to Terms and Conditions - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y << Subscriber to Newsletter Which names would you like to activate HTTPS for? - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 1: www.itzgeek.net - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Select the appropriate numbers separated by commas and/or spaces, or leave input blank to select all options shown (Enter 'c' to cancel): 1 << Choose Site to Install Let's Encrypt Obtaining a new certificate Performing the following challenges: http-01 challenge for www.itzgeek.net Waiting for verification... Cleaning up challenges Deploying Certificate to VirtualHost /etc/nginx/conf.d/www.itzgeek.net.conf Please choose whether or not to redirect HTTP traffic to HTTPS, removing HTTP access. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 1: No redirect - Make no further changes to the webserver configuration. 2: Redirect - Make all requests redirect to secure HTTPS access. Choose this for new sites, or if you're confident your site works on HTTPS. You can undo this change by editing your web server's configuration. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Select the appropriate number [1-2] then [enter] (press 'c' to cancel): 2 << Redirect HTTP to HTTPS Redirecting all traffic on port 80 to ssl in /etc/nginx/conf.d/www.itzgeek.net.conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations! You have successfully enabled https://www.itzgeek.net You should test your configuration at: https://www.ssllabs.com/ssltest/analyze.html?d=www.itzgeek.net - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at: /etc/letsencrypt/live/www.itzgeek.net/fullchain.pem Your key file has been saved at: /etc/letsencrypt/live/www.itzgeek.net/privkey.pem Your cert will expire on 2019-10-28. To obtain a new or tweaked version of this certificate in the future, simply run certbot again with the "certonly" option. To non-interactively renew *all* of your certificates, run "certbot renew" - Your account credentials have been saved in your Certbot configuration directory at /etc/letsencrypt. You should make a secure backup of this folder now. This configuration directory will also contain certificates and private keys obtained by Certbot so making regular backups of this folder is ideal. - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le
Redirect non-www HTTP requests to www HTTPS with Nginx (optional)
We will now configure Nginx server to redirect the traffic comes for non-www HTTP site to the WW HTTPS site, I.e., https://itzgeek.net >> https://www.itzgeek.net.
Here, we will edit the same configuration file that we created for HTTP version of the site.
sudo nano /etc/nginx/conf.d/www.itzgeek.net.conf
Add the below information at the end of the file.
# Redirect NON-WWW HTTP to WWW HTTPS
server {
if ($host = itzgeek.net) {
return 301 https://www.itzgeek.net$request_uri;
}
server_name itzgeek.net;
listen 80;
return 404;
}
Restart the Nginx service.
sudo systemctl restart nginx
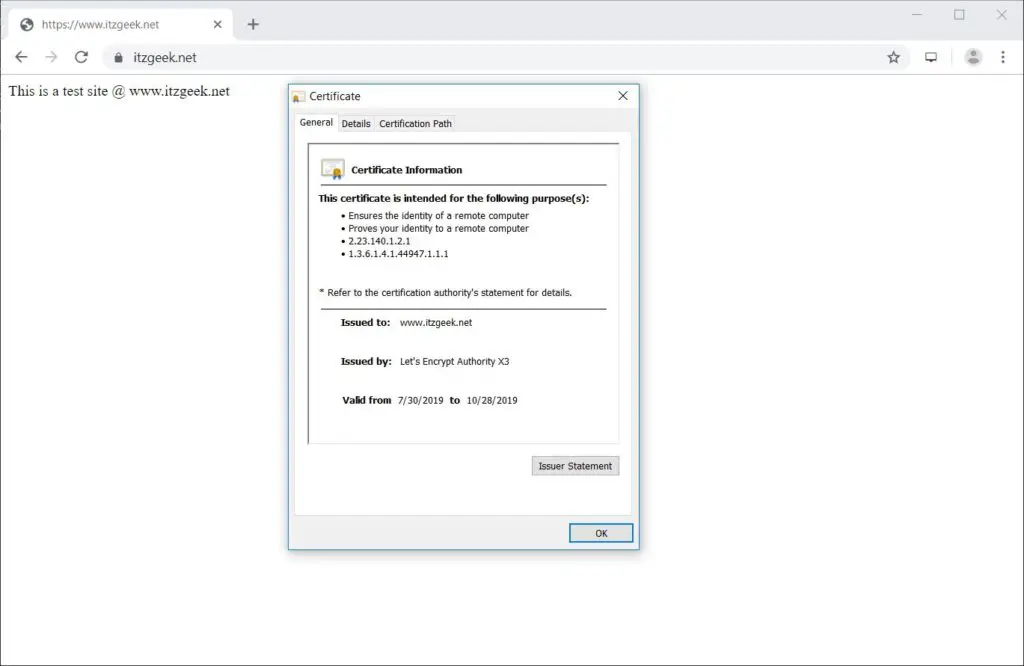
Verify Let’s Encrypt Certificate
Verify the Let’s Encrypt certificate by visiting your website.
OR
You should get HTTPS version of your site now.
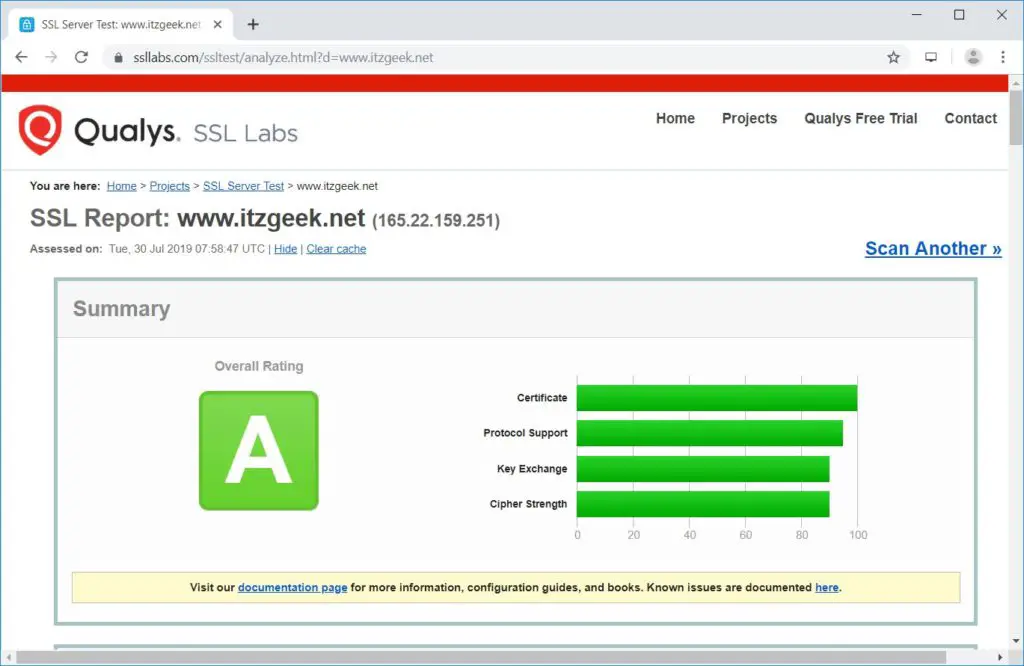
Test SSL Certificate
Test your SSL certificate for any issues and its security ratings by going to the below URL.
Renew Let’s Encrypt Certificate
Let’s Encrypt certificates have a validity of 90 days, and it is highly advisable to renew your certificates before they expire. Thanks to the built-in scheduler entry /etc/cron.d/certbot which runs twice a day to renew certificates which are about to expire.
But, I recommend you to run a below command to simulate automatic renewal of your certificate.
sudo certbot renew --dry-run
Output:
Saving debug log to /var/log/letsencrypt/letsencrypt.log - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Processing /etc/letsencrypt/renewal/www.itzgeek.net.conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Cert not due for renewal, but simulating renewal for dry run Plugins selected: Authenticator nginx, Installer nginx Renewing an existing certificate Performing the following challenges: http-01 challenge for www.itzgeek.net Waiting for verification... Cleaning up challenges - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - new certificate deployed with reload of nginx server; fullchain is /etc/letsencrypt/live/www.itzgeek.net/fullchain.pem - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates below have not been saved.) Congratulations, all renewals succeeded. The following certs have been renewed: /etc/letsencrypt/live/www.itzgeek.net/fullchain.pem (success) ** DRY RUN: simulating 'certbot renew' close to cert expiry ** (The test certificates above have not been saved.) - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - IMPORTANT NOTES: - Your account credentials have been saved in your Certbot configuration directory at /etc/letsencrypt. You should make a secure backup of this folder now. This configuration directory will also contain certificates and private keys obtained by Certbot so making regular backups of this folder is ideal.
If the output confirms that the renewal is working properly, then the automatic renewal will happen as expected.
Conclusion
That’s All. I hope you learned how to Setup Let’s Encrypt SSL Certificate with Nginx on Debian 10. Share your feedback in the comments section.
